The Jolly Roger and the Ransom Note
The Canvas hack disrupted finals week for millions of students, but the economics behind it go back three hundred years.
You’re reading Monday Morning Economist, a free weekly newsletter that explores the economics behind pop culture and current events. Each issue reaches thousands of readers who want to understand the world a little differently. If you enjoy this post, you can support the newsletter by sharing it or by becoming a paid subscriber to help it grow:
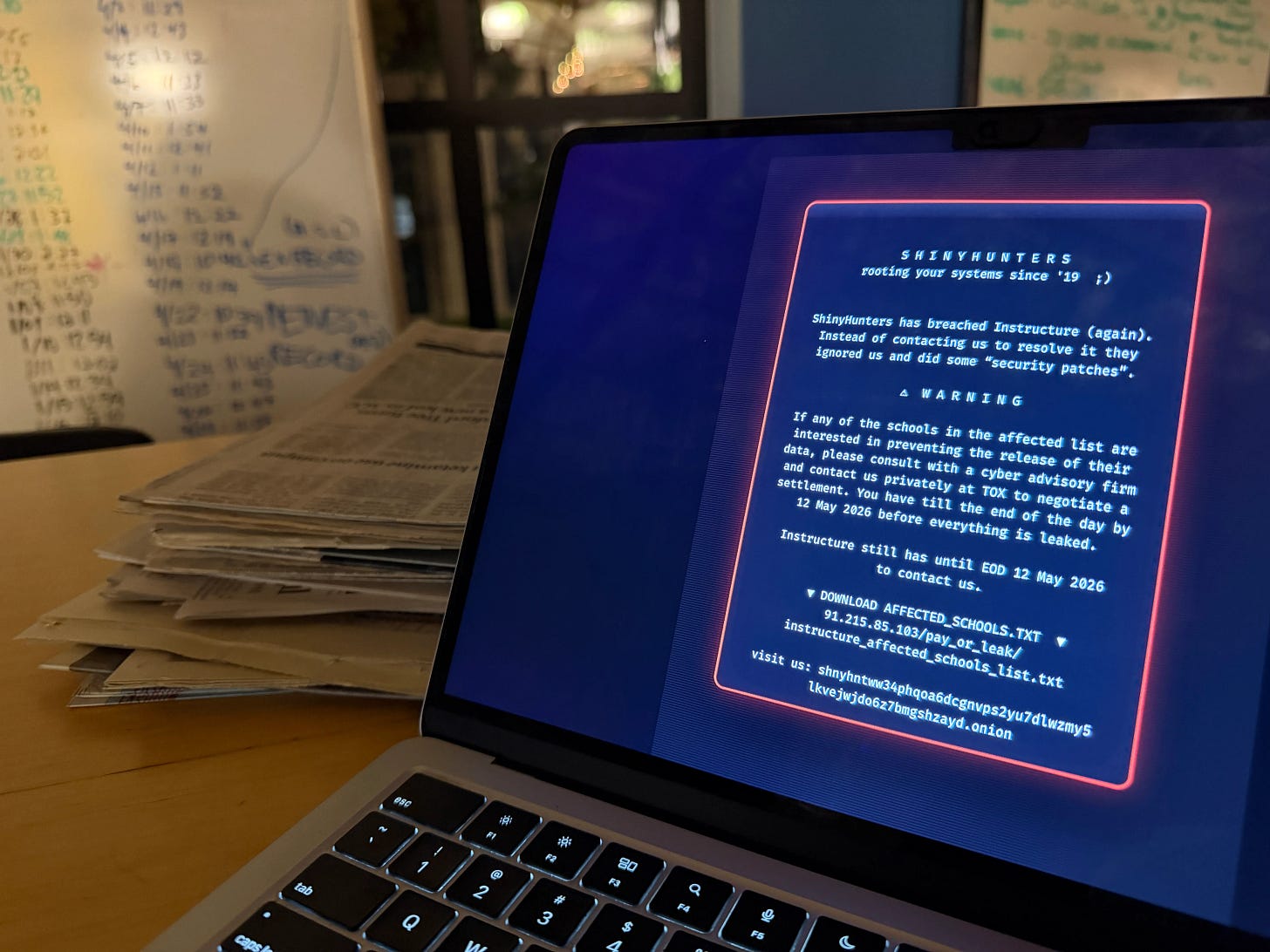
Millions of college students around the country sat down last week to cram for their final exams, but found a ransom letter instead of their lecture notes. A cybercriminal group called ShinyHunters had taken over Canvas, the learning management system used by more than 8,000 schools and 30 million users worldwide.
Students at Harvard, Princeton, Columbia, Georgetown, Penn, and hundreds of other schools were locked out of their coursework, their grades, and their messages with professors. The company that owns Canvas put the platform into emergency maintenance mode while schools scrambled to extend deadlines and shuffle finals schedules.
ShinyHunters gave affected schools until May 12 to negotiate a settlement, or they would leak terabytes of stolen data, including names, emails, student IDs, and messages among users. By Friday morning, most universities were back online. At this time, it’s not clear whether Canvas’s parent company, Instructure, paid a ransom or what the return of Canvas access could mean for the hackers’ May 12 deadline.
You may be wondering why anyone would pay a ransom like this and trust the hackers not to release the data. After all, the hackers are criminals. Couldn’t they just take the money and leak the data anyway? That’s a great instinct, and it’s also the central puzzle that other criminals faced hundreds of years ago.
The trust problem
This wasn’t a traditional ransomware attack, where hackers lock you out of your own systems and sell you the key back. ShinyHunters claimed they already had terabytes of data ready to leak online. What they were trying to sell was a promise: pay us, and we won’t publish it.
That makes it a market. But it’s a market with two pretty fatal design flaws.
First, the attackers need victims to believe the threat is real. If the company suspected the attackers were bluffing about the data they claimed to have, there would be no reason to come to the table at all. The victims also need to believe that paying actually buys something. That’s harder to prove. If ShinyHunters took the money and leaked the data anyway, paying the ransom was a waste. The attackers need to be credible in two ways: credible that they will leak if their demands aren’t met, and credible that they won’t if the ransom is paid.
In most legal markets, this trust is much easier to come by. If a seller scams you, you can sue them, report them to regulators, or leave a bad review online. But here there’s no court, no contract, and no consumer protection agency. The buyer has zero legal recourse.
Economists call this a credible commitment problem. For a deal to work, both sides need to believe the other will follow through. After all, if one side can cheat with zero consequences, why wouldn’t they? If you’ve taken a game theory class, you’ve seen this structure before: it’s the one-shot prisoner’s dilemma. The market should collapse under the weight of its own untrustworthiness. And yet it doesn’t. So how does the business model survive?
The pirate solution
The answer takes us, improbably, to the golden age of piracy. Pirates in the 1700s faced essentially the same credible commitment problem that groups like ShinyHunters face today. They operated entirely outside the law. They couldn’t enforce contracts in court. And their business model had a serious vulnerability: fighting was terrible for business.
This is just one aspect that people get wrong about pirates. The goal was never to battle it out on the open sea. A fight with a merchant crew risked losing men, cargo, and potentially the entire vessel. Pirates actually wanted a quick surrender where goods were handed over, and everyone sails away intact. The offer of surrender only works if the merchant crew believes they will be unharmed after handing off the goods. A pirate captain known for slaughtering crews after they surrendered would find that future targets had nothing to lose by fighting to the death. A broken promise today guaranteed a bloody, expensive battle next time around.
This is where the Jolly Roger comes in. The skull-and-crossbones flag was so widely recognized that merchant crews knew exactly what it meant the moment it appeared on the horizon: surrender your cargo, and we’ll let you live. The flag was a signal, but a signal only works when the reputation behind it is believable. Pirates understood the logic held up only as long as the promise was honored.
Individual pirate captains took it a step further by flying their own distinctive flags. A merchant crew that spotted Blackbeard’s flag knew what to expect based on Blackbeard’s specific track record, not just pirates in general. The personal flag attached a name to the promise, and that made the commitment credible.
ShinyHunters operates on exactly the same premise. The group’s name on the ransom note functions like a pirate flag. The group has previously hit AT&T, Ticketmaster, Santander, Coinbase, and now Canvas. When AT&T reportedly paid $370,000 to have stolen data deleted, the data appears to have actually been deleted.
That matters a lot, not because of what it meant for AT&T, but because of what it signals to the next target. The moment a group becomes known for taking the money and leaking data anyway, the signal becomes useless. Future victims refuse to pay, and the revenue stream dies.
Final Thoughts
Hitting Canvas during finals week wasn’t an accident. A university in the middle of summer break might shrug off a few days of downtime. A university with students mid-exam, panicking, unable to access their lecture materials, has an extraordinarily high willingness to pay. ShinyHunters identified the moment when the demand curve for “getting Canvas back” was at its steepest.
We’ve only barely scratched the surface of what pirates can teach us about economic issues facing organizations. Pirate crews wrote constitutions, elected their captains democratically, and divided loot according to transparent formulas. They did all this to solve problems that look remarkably familiar to us today. If you want to go deeper, Peter Leeson’s The Invisible Hook is a fascinating read that uses pirate governance to illuminate how markets, incentives, and institutions worked out on the open seas.
To be clear, none of this should be taken to indicate that cybercrime is admirable. It’s extortion, and it causes real harm. But if you want to understand how the world actually works, you have to be willing to analyze systems that exist outside polite boundaries. This was a market with supply and demand, pricing strategies, reputation mechanisms, and repeated-game dynamics. The fact that it’s illegal doesn’t make it less of a market.
Know someone who survived the Canvas outage last week? They might want to know the economics behind it. Share this article or forward it to a friend.
Canvas is used by 41% of higher education institutions across North America to deliver courses [Inside Higher Ed]
ShinyHunters wrote on a threat intelligence website that the initial breach involved data from 275 million students, teachers, and staff at nearly 9,000 schools worldwide [NPR]
Ransomware hackers raked in a record $1 billion from victims in 2023 [NBC News]
The Golden Age of Piracy spanned the period from approximately 1650 to 1726 [Library of Congress]
If the black Jolly Roger was insufficient to make a ship surrender, flying a red flag meant the pirates would fight to the death to capture their target [Royal Museum Greenwich]





The Invisible Hook sounds like a very fun book. At the risk of sounding old and cranky, this incident brings nostalgia for the days when professors with some technical know-how hosted their own sites with all the notes, problem sets, their papers, and if you're lucky, some family photos!